A firewall enabled in your environment may block traffic on ports used by Recovery Manager for Active Directory (RMAD), preventing you from backing up or restoring data. Before you start using RMAD, make sure your firewall does not block traffic on ports used by RMAD. For more information about these ports, see the Deployment Guide supplied with this release of RMAD.
This section provides instructions on how to configure the built-in Windows Firewall enabled on Windows Server® 2008 R2 or higher domain controllers in a domain or forest you want to recover, so that RMAD could recover that domain or forest. To ensure a successful recovery, create the following Windows Firewall security rules on all Windows Server® 2008 R2 or higher domain controllers in the domain or forest (leave the default values for settings not mentioned below):
Rule 1a (inbound)
- Rule type: Custom
- Program path: %SystemRoot%\System32\Svchost.exe
- Service settings: Windows Management Instrumentation (Winmgmt)
- Protocol: TCP
- Local ports: Any
- Remote ports: Any
- Local IP addresses: Any
- Remote IP addresses: Any
- Action: Allow the connection
- Rule profile: Domain, private, and public
- Allowed users: Any
- Allowed computers: Any
PowerShell for the Rule 1a settings: New-NetFirewallRule -DisplayName "Rule 1a" -Group RMAD -Enabled True -Profile Any -Direction Inbound -Protocol TCP -Program "%SystemRoot%\System32\Svchost.exe" -Service WMI
Rule 2a (inbound)
- Rule type: Custom
- Program path: System
- Service settings: Apply to all programs and services
- Protocol: TCP
- Local ports: 445
- Remote ports: Any
- Local IP addresses: Any
- Remote IP addresses: Any
- Action: Allow the connection
- Rule profile: Domain, private, and public
- Allowed users: Any
- Allowed computers: Any
PowerShell for the Rule 2 settings: New-NetFirewallRule -DisplayName "Rule 2a" -Group RMAD -Enabled True -Profile Any -Direction Inbound -LocalPort 445 -Protocol TCP -Program System
Rule 3a (inbound)
- Rule type: Custom
- Program path: <Product installation folder>\FRRestoreService64.exe
The default product installation folder is %ProgramFiles%\Quest\Recovery Manager for Active Directory Forest Edition.
- Service settings: Apply to all programs and services
- Protocol: TCP
- Local ports: RPC dynamic port range
- Remote ports: Any
- Local IP addresses: Any
- Remote IP addresses: Any
- Action: Allow the connection
- Rule profile: Domain, private, and public
- Allowed users: Any
- Allowed computers: Any
PowerShell for the Rule 3a settings: New-NetFirewallRule -DisplayName "Rule 3a" -Group RMAD -Enabled True -Profile Any -Direction Inbound -LocalPort RPC -Protocol TCP -Program "%ProgramFiles%\Quest\Recovery Manager for Active Directory Forest Edition\FRRestoreService64.exe"
Note: If the Online Restore Agent uses a specific TCP port then specify the TCP port in the LocalPort parameter. If the RPC dynamic port range is used then specify the RPC dynamic port range in the LocalPort parameter.
Rule 4a (inbound)
- Rule type: Custom
- Program path: %SystemRoot%\System32\Svchost.exe
- Service settings: Remote Procedure Call (RpcSs)
- Protocol: TCP
- Local ports: RPC dynamic port range
- Remote ports: Any
- Local IP addresses: Any
- Remote IP addresses: Any
- Action: Allow the connection
- Rule profile: Domain, private, and public
- Allowed users: Any
PowerShell for the Rule 4a settings: New-NetFirewallRule -DisplayName "Rule 4a" -Group RMAD -Enabled True -Profile Any -Direction Inbound -LocalPort RPCEPMap -Protocol TCP -Program "%SystemRoot%\System32\Svchost.exe" -Service RpcSs
For more information about RPC dynamic port range, refer to the following Microsoft Support Knowledge Base articles at https://support.microsoft.com:
How to configure RPC to use certain ports and how to help secure those ports by using IPsec
How to configure RPC dynamic port allocation to work with firewall
The default dynamic port range for TCP/IP has changed in Windows Vista and in Windows Server® 2008
When planning for Active Directory® forest recovery, you should first have a detailed topology map of your forest. The map should list all the information about the domain controllers, such as their names, FSMO roles, backup status, and the trust relationships between them.
| IMPORTANT |
Make sure that Forest Recovery Agents are installed and function properly on all domain controllers in the forest. |
Because of the complexity and critical nature of the forest recovery process, it is strongly recommended that Active Directory® administrator observe the following rules to prevent the forest failure:
Use only reliable and tested hardware, such as hard disks and uninterruptible power supply.
Test any new configuration in a test lab before deploying it in your environment.
Ensure that each domain in the forest has at least two domain controllers.
Keep detailed logs about the health state of Active Directory® on a daily basis, so that in case of a forest-wide failure the approximate time of failure can be identified.
Regularly back up all domain controllers in the forest with Recovery Manager for Active Directory.
Use the Forest Recovery Console to create a recovery project for your forest. Verify the settings of your forest recovery project on a regular basis, especially when there are membership changes to the Enterprise Admins or Domain Admins group. This helps ensure that the IT staff fully understands the forest recovery plan.
Recovery Manager for Active Directory allows you to restore a domain in the forest to its state at the time of the last trusted backup. Consequently, the restore operation will result in the loss of at least the following Active Directory® data:
All objects (such as users and computers) that were added after the last trusted backup.
All updates made to existing objects since the last trusted backup.
All changes made to either the configuration partition or the schema partition in Active Directory® (such as schema changes).
Additionally, any software applications that were running on the domain controllers will need to be reinstalled on the domain controllers after the forest is recovered.
To restore domain controllers, you can use backups created with Recovery Manager for Active Directory. For this reason, you should back up domain controllers in the forest on a regular basis using one of these applications.
It is a good practice to create a Computer Collection that includes all domain controllers in the forest and back up the Collection each time you make changes to the forest infrastructure. Besides, you can use the Computer Collection to ensure that Forest Recovery Agent is installed on each domain controller in the Collection.
For more information about using the Forest Recovery Agent and Computer Collections, see the User Guide supplied with this release of Recovery Manager for Active Directory.
Before starting a forest recovery operation, you should specify a method for selecting a preferred DNS server for each domain controller in your recovery project.
Select the General tab, then at the bottom see Additional Setting | Preferred DNS and click on the Change button.
You can choose one of the following DNS server selection methods:
Select a DNS server automatically
Let Recovery Manager for Active Directory automatically select a DNS server (used by default).
Do not change DNS settings
Recovery Manager for Active Directory retains client DNS settings during recovery or restores the DNS settings from a backup depending on the chosen recovery method.
Use the specified DNS server
Specify a DNS server manually - here you can specify one DNS address or a list of DNS servers separated by semicolons or using the Edit button.
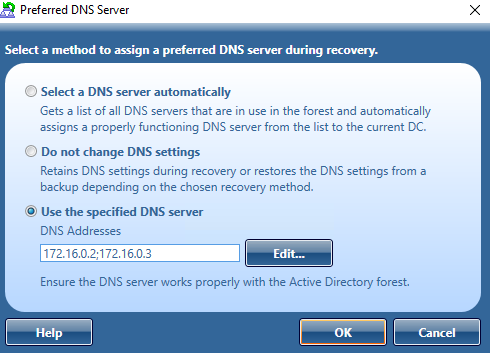
For more information on how to specify a DNS server selection method, see Domain controller recovery settings and progress.
When you choose to select a DNS server automatically, Recovery Manager for Active Directory (RMAD) retrieves a list of DNS servers used by domain controllers. In live Active Directory, RMAD connects directly to domain controllers to get DNS servers that are currently in use. For every recovery method that uses clean OS, current DNS client settings are ignored. With the exception of the Restore Active Directory on Clean OS recovery method which installs the DNS server on the target machine.
The automatic DNS selection method is recommended in the following cases:
Your DNS is not Active Directory-integrated.
Your DNS is Active Directory-integrated and you restore from backups the DNS servers (domain controllers) that act as the primary source for each DNS zone.
For DNS that is not Active Directory-integrated (external DNS), the list of automatic DNS servers is ordered. First come the IP addresses that are included in the DNS client settings on this domain controller. Then, the list includes preferred DNS addresses of other domain controllers in the same domain and their DNS client settings. Then, the same approach is used for domain controllers in the parent domain hierarchy, then in sibling domains, and finally, for direct child domains. Then, during recovery, RMAD automatically selects a properly working DNS server from the received list and assigns that DNS server to the domain controller.
For DNS that is Active Directory-integrated, RMAD first selects DNS servers that are in the same domain. The DNS servers are ordered based on the domain hierarchy from current domain up to root in domain hierarchy. The primary DNS server is selected based on client settings and the most used DNS server in the backup for the DNS zone. The preferred DNS server’s IP address client settings is set on all restored Domain Controllers as the preferred address of the DNS server for the zone the Domain Controller is hosted in. For alternate DNS servers, we obtain a list of other DNS servers which host the DNS zone.
For DNS zones which are forest wide replicated the preferred DNS Server is chosen from the root domain. The same DNS server which is selected as primary for root domain will also be the primary DNS server for any DNS zone which is configured for forest wide replicated.
If a domain controller is a DNS server itself, then a loopback address is included in the DNS server list (see the note below).
By default, the number of DNS servers that can be selected automatically is limited to 3. You can change that number using the MaxAutomaticDnsCount property in advanced settings.
| Important |
It is not recommended to uninstall or reinstall Active Directory on the DNS servers that act as a primary source for an Active Directory-integrated DNS zone. Also, it is not recommended to remove such DNS servers from Active Directory® during recovery . |
The Do not change DNS settings option lets you retain DNS settings during recovery so you do not need to reconfigure DNS settings for each domain controller within the forest after the recovery operation is completed.
When you specify a DNS server or list of DNS servers manually, Recovery Manager for Active Directory first tries to assign the specified DNS server(s) to the domain controller. If the specified DNS server does not function properly or is inaccessible, RMAD automatically selects DNS servers (primary and alternate) that were set on this domain controller before the recovery. If this action is also unsuccessful, RMAD selects DNS servers from a list of all DNS servers that are in use in the forest.
How does RMAD determine that the DNS server is available for use?
Recovery Manager for Active Directory (RMAD) sets a DNS server on all the network adapters on the domain controller and checks if it is enough to register DC Locator resource records and A-type (host) records. If the test succeeds, then this DNS server is set as the preferred DNS server on all network adapters.
| NOTE |
According to Microsoft recommendations, DNS servers should include their own IP addresses in the lists of DNS servers. The loopback address (127.0.0.1) should be configured only as a secondary or tertiary DNS server on a domain controller. If you specified the loopback address in the wrong sequence, the order will be corrected automatically when the list of DNS servers is configured on a domain controller. For more details, see DNS: DNS servers on <adapter name> should include the loopback address, but not as the first entry. |
If you want to use the manual DNS server selection method, it is recommended to make sure you have one or more DNS servers properly configured for working with the domain controllers being recovered. All these DNS servers must support dynamic updates and have DNS zones configured for each domain in the forest you want to recover. Make sure you specify one of these DNS servers for each domain controller in your recovery project.