When a customer signs up for On Demand, they select the region in which to run their On Demand organization. All computation is performed, and all data is stored in the selected region. The currently supported regions can be found here: https://regions.quest-on-demand.com/.
Teams conversation messages intended for processing to rewrite users and teams mentions or attachments links are temporary stored at Azure Virtual Machine disks before being delivered to recipients. The data is encrypted at rest.
Windows Azure Storage, including the Blobs, Tables, and Queues storage structures, are replicated three times in the same datacenter for resiliency against hardware failure. The data is replicated across different fault domains to increase availability. All replication datacenters reside within the geographic boundaries of the selected region.
See this Microsoft reference for more details: https://docs.microsoft.com/en-us/azure/storage/common/storage-redundancy
The most sensitive customer data processed by On Demand Migration for Teams is the content of Teams conversations including file attachments.
To ensure that customer data is kept separate during processing, the following policies are strictly applied in On Demand Migration for Teams:
More information about Azure queues, tables, and blobs:
A common concern related to cloud-based services is the prevention of commingling of data that belongs to different customers. On Demand Migration for Teams has architected its solution to specifically prevent such data commingling by logically separating customer data stores.
Customer data are differentiated using a Customer Organization Identifier. The Customer Organization Identifier is a unique identifier obtained from the Quest On Demand Core that is created when the customer signs up with the application.
This identifier is used throughout the solution to ensure strict data separation of customers' data in Elasticsearch storage and during processing. A separate Elasticsearch server instance is used for each customer.
Internal network communication within Azure includes:
The following scheme shows the communication configuration between key components of On Demand Migration for Teams.
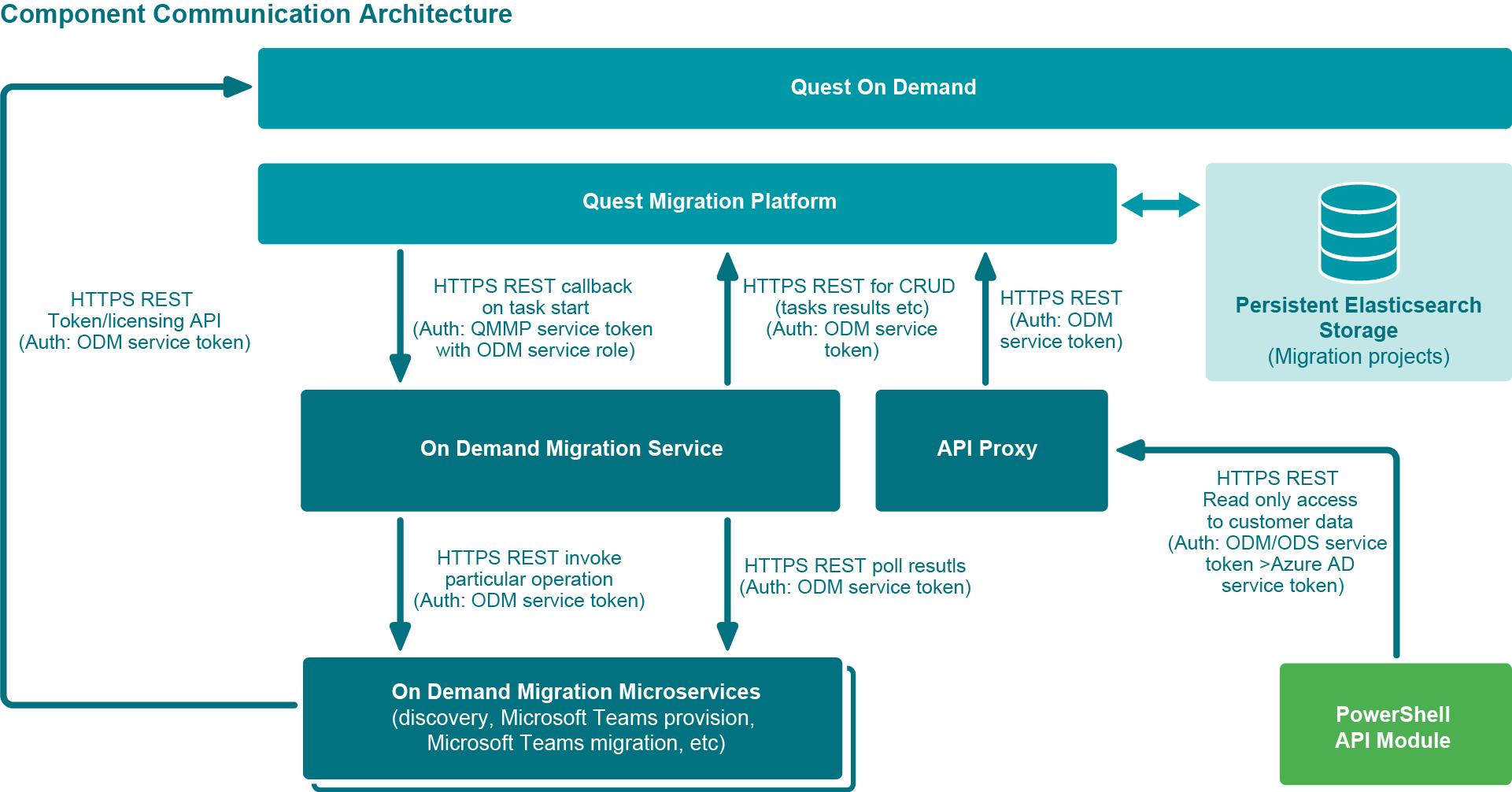
Figure: Component Communication Architecture
The network communication is secured with HTTPS and is not visible to the external public internet.
Inter-service communication uses OAuth authentication using a Quest Microsoft Entra ID service account with the rights to access the services. No backend services of On Demand Migration for Teams can be used by end-users.
On Demand Services accepts the following network communication from outside Azure:
External network communication from outside Azure to On Demand Services include:
All external communication is secured with HTTPS.
The On Demand Migration for Teams user interface uses OAuth authentication with JWT token issued to a logged in user.
PowerShell cmdlets used by Quest Support are using Microsoft Entra ID authentication to access the On Demand Migration for Teams service. The user of the PowerShell API should be a Quest Microsoft Entra ID member with the appropriate role assigned.
There are no unsecured HTTP calls within On Demand Migration for Teams.