System Cache
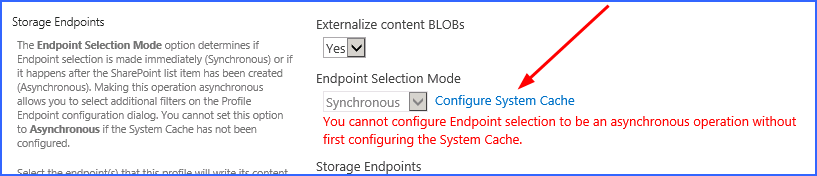
The System Cache enables the creation of asynchronous operations in the storage profile. It can also be used as a backup endpoint if the primary endpoint fails.
The System Cache can be accessed from the main Metalogix StoragePoint menu or from the storage profile page.
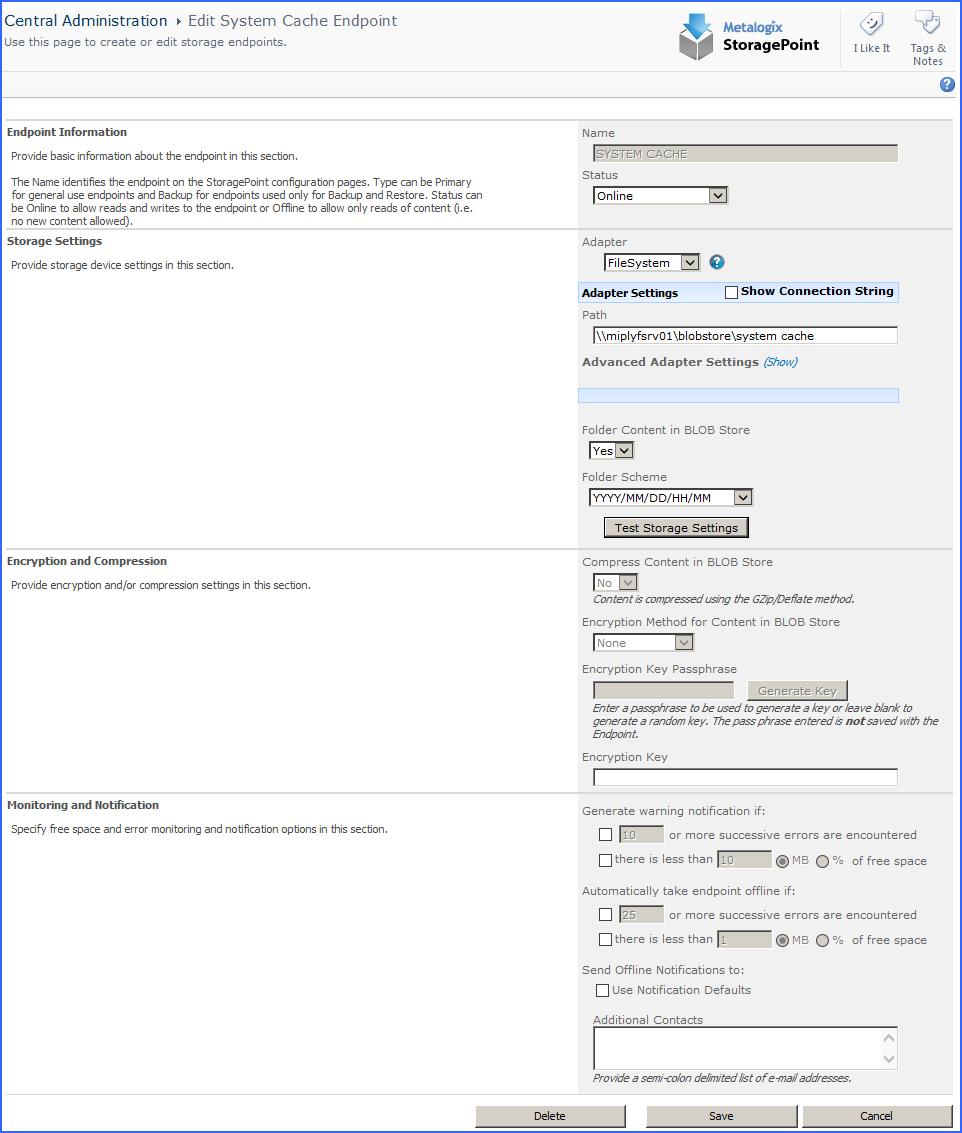
The system cache is configured like most storage endpoints, except that the name cannot be edited. Use the chart below as a guide to complete the system cache settings.
|
Setting |
Value/Options |
|
Endpoint Name |
Read-only field for the name of the storage endpoint. |
|
Status |
Online Storage endpoint should be available to associate to a Storage Profile and accept BLOBs. (default) Offline (Read Only) A storage endpoint can be configured, but not made available for externalizing content. The BLOBs already on the endpoint are still read only. |
|
|
Select the adapter for the endpoint that is being created. The FileSystem adapter is installed with the core product by default. |
|
|
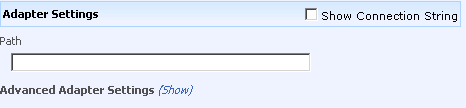
Enter an adapter-specific connection string in this box.
The fields for the Adapter Settings will change depending on the adapter type selected. Please see the specific Adapter Administration Guide for configuring the adapter type selected. |
|
|
No Externalized content BLOBs are not placed in folders. Yes Externalized content BLOBs are placed in folders (default). |
|
|
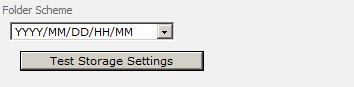
If Folder Content in BLOB Store is Yes, select a date/time folder scheme from the dropdown. YYYY/MM/DD/HH/MM is the default.
|
|
|
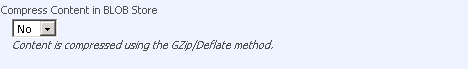
No Externalized content BLOBs are not compressed (default). Yes Externalized content BLOBs are compressed. |
|
|
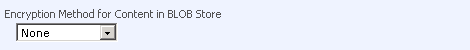
None Encryption will not be applied to externalized BLOBs (default). AES (128 bit) 128 bit AES encryption will be applied to externalized BLOBs. AES (256 bit) 256 bit AES encryption will be applied to externalized BLOBs. |
|
|
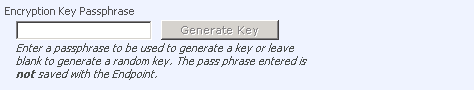
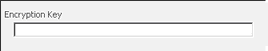
Enter a passphrase to use when generating the encryption key. Using a passphrase will help re-create the encryption key if necessary. A random key is generates by leaving the box blank and clicking Generate Key. |
|
|
This is a read-only box that contains the generated Encryption Key. |
|
|
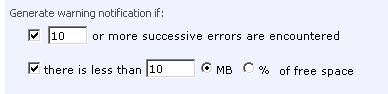
A warning email can be sent if a Storage Endpoint encounters errors or is nearing capacity. |
|
|
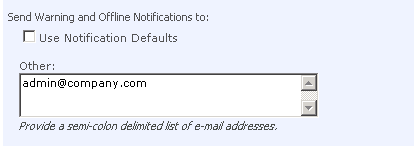
Default email addresses for system error and offline notification can be entered. Check the box to include the list of Default Notification Contacts specified on the General Settings page. |
Creating a New Storage or Backup Endpoint
1.Click the Create New Endpoint link.
2.Complete the fields as appropriate.
3.For assistance on configuring each type of adapter, select the adapter from the dropdown and click the help symbol. This document will show the complete steps for configuring an endpoint.
Compression and Encryption Resource Usage
Metalogix StoragePoint offers the options of compressing and/or encrypting external BLOB files on a given endpoint. The compression option can provide better storage utilization by shrinking files and the encryption option can provide for better security of blob data both during transmission and at rest. However, since both options are implemented in software and not hardware, there is a resource cost associated with using them.
Both software compression and encryption utilize CPU resources. The amount of CPU used for compression varies depending on the size of the files and whether they are already compressed or not (i.e. PDF, DOCX, XLSX, etc.). Larger files and files that are already mostly compressed can utilize substantial CPU resources during compression processing. The amount of CPU used for encryption can increase depending on the size of the file (larger file sizes use more CPU resources).
Here are some general guidelines to consider when deciding whether to use compression and/or encryption on an endpoint:
·If the server or VM environment of the WFE is underpowered - i.e. too few processors/cores allocated, older/slower CPUs, etc. - then consider not using the compression and encryption options. We recommend no fewer than 2 actual cores be dedicated to each WFE if these options are use. Four or more actual cores is preferable.
·If the environment is a VM, ensure that actual CPUs and cores are being dedicated to the VM. A virtual CPU allocated to a VM does not usually map one-to-one to a physical core or CPU. So if a VM host contains 1 CPU with 4 cores and there are 8 VMs running on it, there is not a one-to-one mapping of cores to vCPUs.
·Compression is not effective on files that are already compressed. Note that most PDF files, Office 2007/2010 files and media files (JPEG, MPEG, etc.) may already be internally compressed. If the bulk of files being externalized are these types of files, use of compression should be avoided as it will just waste CPU resources and yield little to no compression.
·Large files (greater than 20 to 30 MB) may take large amounts of CPU to compress. If compression must be enabled, consider tuning the compression setting on the General Settings page. A maximum compression size can be specified that will stop compression for files above a certain size threshold. Also, the overall compression level can be modified to ramp down the amount of compression that will be achieved but also save CPU resources.
·Compression/encryption cannot be changed once the endpoint is saved. To change these settings, the content will need to migrated or recalled, the endpoint deleted, and then recreated with or without the change to the compression/encryption settings.
Editing an Existing Storage or Backup Endpoint
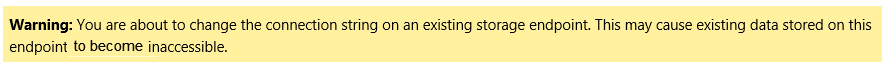
While certain aspects of an active storage endpoint can be modified, one should take care when performing this operation as content can become irretrievable.
|
|
NOTE: Compression and encryption settings on an active storage endpoint cannot be changed. These fields will be disabled. To change these settings, run the Recall or Migration job to move content back into the content database or to another endpoint (decompressing and decrypting it along the way), create a new endpoint with new settings, and then run the Externalize or Migrate job to move the content out of the content database. So plan accordingly. |
1.Open the endpoint by clicking its name on the Storage and Backup Endpoints page.
2.Make the necessary changes. See the chart in the specific adapter guide for clarification on fields.
3.If changes are made to the Adapter or Connection property in the Storage Settings section there will be a warning about the possibility of content becoming irretrievable.
4.Click Save to apply the changes.