The Operations Master service is used to manage and configure plugins. Plugins are Desktop Authority provided objects that the Manager uses to perform specific operations. There are a few default plugins that are necessary for Desktop Authority to collect data and report on it. The Operations Master service object is available exclusively to Super Users/Groups. Non-Super Users/Groups do not have the ability to open the Operations object.
The Operations Master service object list provides the ability to sort the list on any of the three columns, ascending or descending order. The order of the columns themselves can also be changed. Simply drag a column to its new desired location in the list.
Click on any plugin to select it. The Toolbar will become enabled with the necessary buttons.
Select this option from the toolbar to restart the selected service.
Click Edit to modify the selected plugins options.
Instead of waiting for the automatic Profile and RBA Audit data backup, click Synch Reporting Data to process reporting data right away. This button is only available when the ETLProcessor plugin is selected.
Select refresh from the toolbar to update the plugins list.



The ETL processor plugin manages the data collection processes. This plugin is a service that is installed and started when Desktop Authority is installed. This service should run regardless of whether the Manager is running or not. It helps to collect data as users' login and out of the network. Many other user operations are also logged.
User and Computer Data are collected by Desktop Authority's Operations Master service and the ETLProcessor plugin. Data Collection can be configured for both the User and Computer in their respective Data Collection objects. Computer Management Data Collection can be configured for hardware, software, and USB/Port Security. User based Data Collection can be configured for login/logoff and lock/unlock events.
There are several configuration parameters available for this plugin. Click Edit to modify the plugin details.
Specify the amount of time (in minutes) for the data collection and processing threads wait after they finish. The default sleep time is set to 15. Allowable values can be between 1 and 60 minutes.
Specify the time of day for the configuration data to be processed and moved to the Reporting database. Once the data resides in the Reporting database it can be reported on. Database maintenance is also performed at this time (removing old records), which is based on the Retention period for database records setting. The default time is set to 4:00 AM.
The Operations Service recycle time is automatically configured to be 15 minutes prior to the time specified here.
Specify the number of days in which malformed collection data files can be purged. The default value is set to 10 days but may be changed to any value between 0 and 30 days.
Certain configuration data tables grow at a very fast rate. This necessitates the ability to purge older data from the system. The default retention period is set to 180 days. This may however be set to any value between 0 and 360 days.
Click Save to commit all changes to the ETLProcessor plugin configurations.
Click Cancel to go back to the last saved values of all ETLProcessor plugin configurations.
This service is a background service that is used to manage and configure Desktop Authority's plugins. These plugins are used to perform specific operations such as audit data collection and the execution of scheduled reports.
User and Computer Data is collected by Desktop Authority's Operations Master service and the ETLProcessor plugin.
Data Collection can be configured for both the User and Computer in their respective Data Collection objects. Computer Management Data Collection can be configured for hardware, software and USB/Port Security. User based Data Collection can be configured for login/logoff and lock/unlock events.
Select the Operations Master Service plugin by clicking on it. When selected, its color will be highlighted. Click Edit to change the service credentials for this plugin, Enter the User name and password credentials. The User name must be entered in the form of Domain\Username.
|
|
Note: The Operations Master service requires a user account that belongs to the Domain Admins group. |
The ReportScheduler plugin runs scheduled reports. This plugin runs every 10 minutes, by default, checking for reports to run. The timing interval may be changed in the Desktop Authority Setup tool.
The Replication Options dialog box provides several options and preferences.
Specify the server that the Desktop Authority configurations are replicated from. By default, this is where the Manager is installed to.
Specify the folder that User Management configurations are replicated from. By default, this is the NETLOGON location, shared by the installation as SLSCRIPTS$.
Specify the folder that Computer Management configurations are replicated from. By default, this is the DADevicePolicyMaster$ share.
Select this check box to include all hidden and system files that exist in the source folder in the replication copy. Clear this check box to leave all hidden and system files in the source folder.
Select this check box to overwrite any files marked as read-only in the destination folder with a new file from the source folder. Clear this check box to leave all original read-only files intact.
Select this check box to include all sub-folders found in the source folder in the replication copy. Clear this check box to suppress the copy of sub-folders.
Select this check box to continue to replicate files even if an error occurs while copying files. Clear this check box to stop replicating files if an error occurs.
|
|
Note: Please refer to the File Paths appendix for the correct path(s) based on the version of Desktop Authority you are using. |
Specify a folder that will hold the User Management replicated configurations. By default, this is the NETLOGON share.
Specify a folder that will hold the Computer Management replicated configurations. By default, this is the SYSVOL\[Domain]\Policies\Desktop Authority\Device Policy Master folder.
Desktop Authority will attempt to connect to either the DA Administrative Service or the Update Service on the user's logon server (the server where slogic.bat is executed from, upon logon). If the requested service does not respond, or is not installed on that server, Desktop Authority will use a default site map to locate a server that has an active and responsive service. The default site map is created based on the information in the Server Manager list, and groups all servers to their respective site. The default site map will instruct Desktop Authority to attempt to connect with the service on one of the other server(s) that are listed in the same site as the workstation's site.
If for some reason, Server Manager does not include any servers within the workstation's defined site, or there is no available service to connect to in the list of servers on the site, Desktop Authority will then randomly select a server from the Server Manager list.
The default site map can be customized to utilize the enterprise's topology. Select Custom to customize the default site map settings.
Select this option to use the site map that is created by default by Desktop Authority. This option will try to locate a responsive service on the DA login server first, look to the default site map and check other servers on the same site as the workstation. As a last resort, Desktop Authority will randomly select a server from the Server Manager list.
Select this option to define a custom site map for specific to the enterprise's topology. Selecting this option will enable the Site Map grid and allow for changes to it. The default site map configuration will appear in the grid, before any changes are made.
Select this option to disable the site map functionality of Desktop Authority. When not using a site map, default or custom, Desktop Authority will first try to locate a responsive service on the DA login server. If the service does not respond, then a random server will be selected from the Server Manager list until a responsive service is found.
This option is selected by default. This instructs Desktop Authority to check for a responsive DA Administrative Service on the login server first. The servers on the site of the workstation with the request will be recursed first.
This option will disregard any sites specified on a server entry. This will disable the ability to link the sites recursively.
The use of server caching will force Desktop Authority to remember the last server where a responsive DA Administrative Service was found and to use that one for the next request, even if the next request is completed during another session. If this option is not selected, the cache will not be used. This will cause Desktop Authority to walk through the rules for finding a responsive service each time a request is made.
Enter the number of days the cache should be reset on. The default cache days are 5. This means, every 5 days, the cache will be reset (the servers will be walked through every 5 days). Enter 0 to disable the number cache days, and to always remember the last responsive server found.
Select this box to have Desktop Authority randomly choose a server from the server manager list if all servers within the specific site fail to give a response to indicate that it is accessible.
Select Custom from the site map configuration options. This will present an editable grid, where you can build your custom site map.
Click Add Site to add a new site to the site map list. Select a known site from the drop list. Click Edit Site to edit the selected site. Click Delete Site to remove a site from the custom site map.
Select *DEFAULT from the drop down list to create a custom defined default site list. The custom defined default site list is one that is used as a catch all for any workstation that does not have a site defined for it. It is added to the custom site map with a site name of *DEFAULT.
When modifying the Site list (Add or Edit site mode), the Server/Site list will be available for modification. This is where the entries for the selected Site will be added.
Click Add Server, Add Site, and Delete Entry to update the entry list. An asterisk (*) will be automatically pre-pended to any site name in order to distinguish it from a server entry.
Click Save to save the Custom Map changes. Click Cancel to exit without saving changes.
Let's assume first that Workstation124, in the Tampa site, makes a request of the DA Administrative Service. Since Workstation124 ran slogic.bat from server Tampa-MS1, DA will attempt to connect to the DA Administrative Service on Tampa-MS1.
Figure 28: Example site map
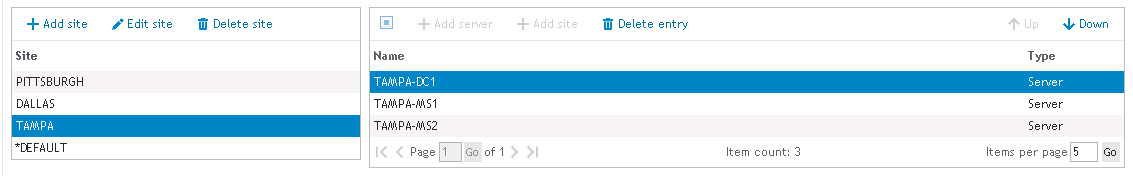
If the login server is unresponsive or the Check login server first option is unchecked, the site that the workstation belongs to will be discovered. The servers within the site will be checked in order until a responsive server is found. In this example, this means that the Tampa site will be discovered from the workstation. The next servers to be checked will be Tampa-DC1 and Tampa-MS2, respectively.
If all of the servers in the Tampa site fail, the example custom site map is configured to continue searching on the Dallas site. This is denoted with the Dallas site entry in the Tampa site map. However, if the Site recursion option is unchecked, the *Dallas entry in the site map will be disregarded.
If all sites and servers defined in the Tampa custom site map are exhausted, the default setting of the Randomly failover if site server is not available option (checked), takes over and servers listed in Server Manager will be randomly chosen until a responsive server if found. Keep in mind that no server will be checked more than once per request. If this option is not checked, a responsive server will not be found and the service request will fail.
In this next example, Workstation1 makes a DA Administrative Service request. Workstation1 has no default site defined. Since Workstation1 ran slogic.bat from server MS3, DA will begin with an attempt to connect to the DA Administrative Service on the MS3 server. If the attempt fails, since there is no default site definition for the workstation, the servers specified for *DEFAULT will be used to look for a responsive service. Remember that the *Default site does not exist unless it was added to the custom site map by adding as a site.
Figure 29: Example site map
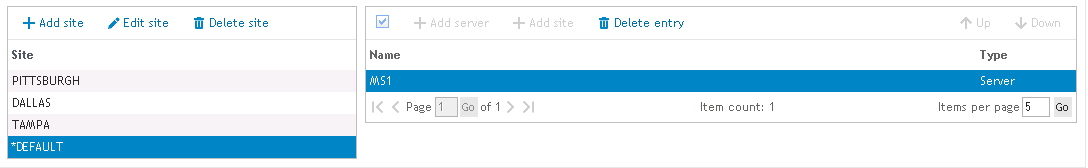
If the Check login server first is unchecked, the system will go right to the servers defined in the *DEFAULT section of the custom site map.
If the Randomly failover if site server is not available box is not selected, then the service request will immediately fail as the options do not allow the request to search for a responsive server.
The Client Deployment object provides access to the Assign Script object and the GPO Deployment object, both of which arm the domain user and computer with configurations for Desktop Authority to execute during client logon process.
The Assign Script object is used to assign the SLOGIC logon script to domain user accounts for User Management profiles and objects.
The GPO Deployment object provides the ability to deploy Desktop Authority's SLagent technology to client workstations by using a GPO extension.
Client Provisioning encompasses both GPO Deployment and Logon-based Deployment and dynamically chooses from the best of several deployment approaches at runtime in order to deploy necessary files to the client computer.
Off-Network Support (ONS) allows computers to receive configuration updates over the internet without having an active connection to the parent domain. Off-Network Client Provisioning (ONCP) allows for the initial provisioning of new computers to occur off-network (i.e. while being disconnected from the parent domain). Once a new off-network computer has been provisioned using ONCP, it is immediately ready to begin retrieving Off-Network Desktop Authority settings (assuming an active internet connection and ONS being configured).
However, unlike the automated on-network provisioning process, ONCP deployment can only be done outside of the Desktop Authority framework. This means Admins attempting to utilize ONCP MUST first determine an efficient method to deploy and install the necessary files to their off-network computers that require Desktop Authority provisioning.
|
|
IMPORTANT: Microsoft .NET Framework 4.6 (or 4.5) must be installed and enabled on client computers prior to provisioning using ONCP. Desktop Authority will not function correctly on computers provisioned using ONCP without a supported version of .NET already installed and enabled. In the case of computers provisioned on-network, a supported version of .NET is automatically installed if needed. |
|
|
NOTE: Both files MUST be located in the same folder prior to installation. |