In general, a forest recovery is necessary if none of the domain controllers in the forest can function normally or if the corrupted domain controllers can spread dangerous data to other domain controllers. Some examples of forest-wide failures include:
None of the domain controllers can replicate with its replication partner.
Changes cannot be made to Active Directory® at any domain controller.
New domain controllers cannot be installed in any domain.
All domain controllers have been logically corrupted or physically damaged to a point that business continuity is impossible (for instance, all business applications that depend on Active Directory® are non-functional).
A rogue administrator has compromised the Active Directory® environment.
An adversary intentionally or an administrator accidentally runs a script that spreads data corruption across the Active Directory® forest.
An adversary intentionally or an administrator accidentally extends the Active Directory® schema with malicious or conflicting changes.
| Important |
When you encounter the symptoms of a forest-wide failure, work with Microsoft Customer Support Service to determine the cause of the failure and evaluate any possible remedies. Because of the complexity and critical nature of the forest recovery process, the recovery of the entire Active Directory® forest should be viewed as a last resort. Please consult Microsoft Customer Support Service before you take a definitive decision. |
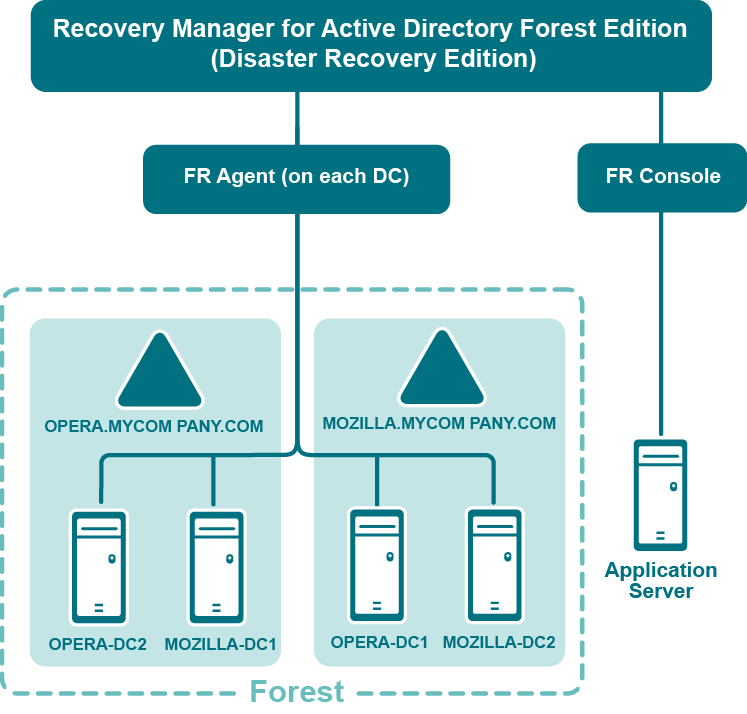
The following diagram shows the Recovery Manager for Active Directory Forest Edition (Disaster Recovery Edition) deployment:
Recovery Manager for Active Directory is designed to ensure intuitive operation and close integration with the Windows® operating system.
The best practice is to install the Forest Recovery Console on a standalone computer. This allows you to avoid situations where a corruption in Active Directory prevents you from using the Forest Recovery Console. But if you install Recovery Manager for Active Directory on a machine within a domain, it is recommended to use local Administrative credentials (non-AD user account) to access the Forest Recovery Console machine.
Have Read access to the Recovery Manager for Active Directory backup registration database.
Be a member of the Domain Users group on each target domain.
Be a member of the local Administrators group on the target domain controller.
The best practice is to use a local user account instead of domain credentials to access a backup. This allows you to avoid problems with access to the backup storage when domain controllers are not available during recovery.
The account under which you run Forest Recovery Console or the account that is configured for scheduled verification should have:
Read access to the backup database
Be a member of the local Administrators group on the target domain controller
Write access to the debug logs folder (Optional)
For more details, refer Checking forest health.
Have either domain administrator rights or all of the following permissions on the container for the test user account:
Create/Delete user objects Applies to: This object and all descendant objects
Full Control
Applies to: Descendant User objects
For information about using the Forest Recovery Console, see Forest Recovery Console.