-
Title
Internet Explorer or Firefox do not trust the Desktop Authority site -
Description
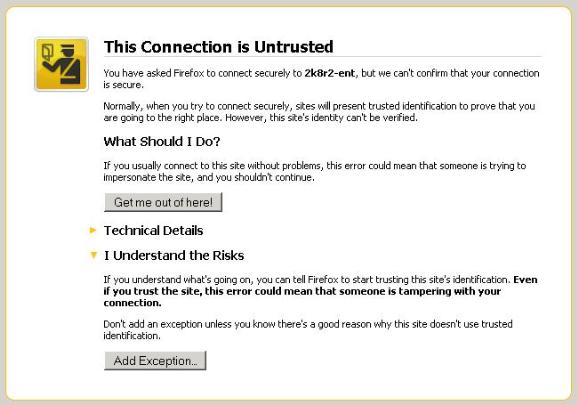
Desktop Authority creates a self-signed certificate during installation but Internet Explorer and Firefox will not see this as a trusted certificate. Therefore the following types of warnings may be seen when loading the DA Manager.
![[image]](https://support.quest.com/KBArticleImages/SL3819/13103b89.jpg)
Sign In Required
You need to be signed in and under a current maintenance contract to view premium knowledge articles.
