Enabling Secure Connect
Secure Connect is enabled through the use of environmental variables on the client machine. No configuration is required on the QoreStor server.
To enable Secure Connect on a Windows client
- On the client server, press Win+R to open the Run window.
- Type sysdm.cpl and click OK.
- Click the Advanced tab, then Environment Variables.
- In the System Variables section, click New.
- In the Variable name field, enter SECURE_CONNECT.
- In the Variable value field, enter one of the following:
- 0 - disables Secure Connect
- 1 - Secure Connect is enabled, but QoreStor will failback to an unsecured connection if the Secure Connect server is unavailable.
- 2 - Secure Connect is enabled. Connection will fail if Secure Connect server is unavailable.
- Click OK, then OK.
|

|
IMPORTANT: After enabling Secure Connect, you will need to change the BypassPorts configuration in the sc_client.properties file. Refer to Configuring Secure Connect properties for information. |
|

|
IMPORTANT: After enabling Secure Connect, you must restart the DMA application services. |
To enable Secure Connect on a Linux client
- At the command prompt on the client machine, enter the following command
echo 'export SECURE_CONNECT=<0|1|2>' >> ~/.bashrc
Where:
- 0 - disables Secure Connect
- 1 - Secure Connect is enabled, but QoreStor will failback to an unsecured connection if the Secure Connect server is unavailable.
- 2 - Secure Connect is enabled. Connection will fail if Secure Connect server is unavailable.
- Log out of the QoreStor system, then log in.
|

|
IMPORTANT: After enabling Secure Connect, you will need change the BypassPorts configuration in the sc_client.properties file. Refer to Configuring Secure Connect properties for information. |
|

|
IMPORTANT: After enabling Secure Connect, you must restart the DMA application services. |
Configuring Secure Connect properties
Before using Secure Connect, ensure that the default port configuration is appropriate for your environment. The ports used by Secure Connect are:
- 9443 - this is the listening port. The Secure Connect server listens for connection requests on this port.
- 10011, 11000 and 9920 - These are the standard Secure Connect communication ports.
By default, the Secure Connect ports are bypassed, which will cause Secure Connect to failback to a normal, unsecured connection. Before using Secure Connect, the BypassPorts setting must be set to 0 to enable full communication.
Secure Connect properties can be configured through the sc_client.properties file located in the client installation directory.
To configure Secure Connect
- In the client installation directory, open the sc_client.properties file with a text editor.
The default installation directory differs depending on the client type and the OS of the client machine. For example,
- The RDA client on a Windows machine installs to C:\Program Files\Quest\RDA\dynlib
- The NetVault on a Linux server installs to /usr/netvault/dynlib/sc_client.properties
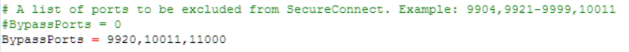
- Find the entry shown below
- Do one of the following:
- Comment out the line BypassPorts = 9920, 10011, 11000 by adding a # to the front, then remove the # from BypassPorts = 0
- Delete the listed ports (9920, 10011, 11000) and replace with 0.
- Save the file.
Managing Secure Connect with plug-in 4.1.0.265 or later
Unless manually disabled, Secure Connect is always running on the QoreStor server. Starting with QoreStor plug-in version 4.1.0.265, Secure Connect is enabled by default on the client machine. Review the sections below for the procedures to check Secure Connect status or disable and enable Secure Connect.
The commands below can be executed both on the QoreStor server and the client machines. In both cases, the sc_manager command must be executed from the directory that includes the sc.client.properties file. By default this is:
- On the QoreStor server /opt/qorestor/bin
|

|
NOTE: When configuring Secure Connect on the QoreStor server, the changes made are applicable only for container or optimized replication in which the QoreStor instance is a source. |
- For client machines, this is the plug-in installation directory. For example, for NetVault Backup:
- Linux clients - /usr/local/ocarda
- Windows clients - C:\Program Files\Quest\RDA\Dynlib
|

|
IMPORTANT: The procedures below use the sc_manager command which must be executed by the root account. |
Checking Secure Connect status
To check the status of Secure Connect
- Execute the command sc_manager status according to one of the methods below:
- The status of Secure Connect will be displayed:
SecureConnect.enabled = true
Disabling Secure Connect
To disable Secure Connect
- Execute the sc_manager disable command as described below:
- The status of Secure Connect will be displayed as confirmation:
SecureConnect.enabled = false
- After disabling Secure Connect, a service restart must be performed.
- If you disabled Secure Connect on the QoreStor server, restart the QoreStor services using the commands:
/opt/qorestor/bin/ctrlrpc -p 9901 node.stop
/opt/qorestor/bin/ctrlrpc -p 9901 node.start
- If you disabled Secure Connect on the client machine, services of the DMA application on that machine need to be restarted.
Enabling Secure Connect
To enable Secure Connect
- Execute the sc_manager disable command as described below:
- The status of Secure Connect will be displayed as confirmation:
SecureConnect.enabled = true
- After enabling Secure Connect, a service restart must be performed.
- If you enabled Secure Connect on the QoreStor server, restart the QoreStor services using the commands:
/opt/qorestor/bin/ctrlrpc -p 9901 node.stop
/opt/qorestor/bin/ctrlrpc -p 9901 node.start
- If you enabled Secure Connect on the client machine, services of the DMA application on that machine need to be restarted.
Adding certificates for Secure Connect
The QoreStor Secure Connect feature requires custom certificates on both the client and QoreStor server machine.
|

|
NOTE: The certificates on both the client machine and QoreStor server must be from the same certificate authority. |
Adding a Secure Connect certificate - Windows Client
- Prepare custom certificates chain and install them to the certificate store using the Microsoft Management Console (MMC) Certificates snap-in.
- Install the Root certificate to Trusted Root Certification Authorities.
- If necessary, install the Intermediate certificate to Intermediate Certification Authorities.
- Install the Server certificate to Personal.
- In the client installation directory, open the sc_client.properties file with a text editor.
- Edit the entries below:
- openSSL.client.caConfig - The path to the file of the trusted root certificate or directory containing the trusted root certificates chain. For specifying directory path, be sure that directory contains certificates in the PEM format and symbolic links to the certificate files, created by the c_rehash utility.
- openSSL.client.certificateFile - The path to the file containing the server's or client's certificate in PEM format.
- openSSL.client.privateKeyFile - The path to the file containing the private key for the certificate in PEM format.
Example in case there is the chain of 3 certificates (root, intermediate, server), private key and they are located in the same directory as sc_client.dll:
- openSSL.client.caConfig = ${application.configDir}
- openSSL.client.certificateFile = ${application.configDir}server-certificate-name.pem
- openSSL.client.privateKeyFile = ${application.configDir}privat-key-name.key
Example in case there is the chain of 2 certificates (root, server), private key and they are located at C:\certificates:
- openSSL.client.caConfig = C:\certificates\root-certificate-name.pem
- openSSL.client.certificateFile = C:\certificates\server-certificate-name.pem
- openSSL.client.privateKeyFile = C:\certificates\privat-key-name.key
- Make c_rehash for the certificates:
- Download perl from https://www.activestate.com/ActivePerl.
- Download the perl script c_rehash, stored inside OpenSSL (https://wiki.openssl.org/index.php/Binaries)
- Set the new openssl environment variable with the path to openssl.
- Run the command prompt.
- Use perl.exe with path_to_the_c_rehash and path_to_the_cert_dir arguments (e.g. perl.exe C:\<path to the c_rehash> C:\<path to the certificates directory>)
- When Secure Connect is used with any DMA - restart DMA services.
|

|
NOTE: If certificate validation fails, the connection between client and server will fail back to a normal connection. |
Adding a Secure Connect certificate - Linux Client and QoreStor server
- Prepare custom certificates chain
- Place the certificate to be trusted (in PEM format) in /etc/pki/ca-trust/source/anchors/ and run sudo update-ca-trust at the prompt.
If the certificate is in OpenSSL’s extended BEGIN TRUSTED CERTIFICATE format, place it in /etc/pki/ca-trust/source and run sudo update-ca-trust.
- Make c_rehash for the certificates:
- Install the openssl-perl package.
- Run c_rehash <path-to-the-folder-with-certificates>.
- In the client installation directory, open the sc_client.properties file with a text editor.
- Edit the entries below:
- openSSL.client.caConfig - The path to the file of the trusted root certificate or directory containing the trusted root certificates chain. For specifying directory path, be sure that directory contains certificates in the PEM format and symbolic links to the certificate files, created by the c_rehash utility.
- openSSL.client.certificateFile - The path to the file containing the server's or client's certificate in PEM format.
- openSSL.client.privateKeyFile - The path to the file containing the private key for the certificate in PEM format.
Example in case there is the chain of 3 certificates (root, intermediate, server), private key and they are located in the same directory with sc_client.so, server side:
- openSSL.server.caConfig = ${application.configDir}
- openSSL.server.certificateFile = ${application.configDir}server-certificate-name.pem
- openSSL.server.privateKeyFile = ${application.configDir}privat-key-name.key
Example in case there is the chain of 2 certificates (root, server), private key and they are located at /usr/certificates on the client machine:
- openSSL.client.caConfig = /usr/certificates/root-certificate-name.pem
- openSSL.client.certificateFile = /usr/certificates/server-certificate-name.pem
- openSSL.client.privateKeyFile = /usr/certificates/privat-key-name.key
- When Secure Connect is used with any DMA - restart DMA services.
|

|
NOTE: If certificate validation fails, the connection between client and server will fail back to a normal connection. |