-
タイトル
Using Record Type in Office 365 Audit Data -
説明
Using Record Type in Office 365 Audit Data -
対策
The Record Type data field in Audit Database is a major addition to the Audit Data Source and is now available.
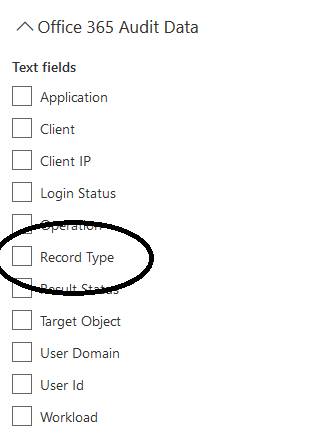
For example you can see just Admin Operations (8) or any file that has been modified (6) or DLP (33).
Here is a list of Record IDs which may be in the audit timeline if that event has been generated
1 – Indicates a record from the Exchange admin audit log.
2 – Indicates a record from the Exchange mailbox audit log for an operation performed on a singled mailbox item.
3 – Also indicates a record from the Exchange mailbox audit log. This record type indicates that the operation was performed on multiple items in the source mailbox (such as moving multiple items to the Deleted Items folder or permanently deleting multiple items).
4 – Indicates a site admin operation in SharePoint, such as an administrator or user assigning permissions to a site.
6 – Indicates a file or folder-related operation in SharePoint, such as a user viewing or modifying a file.
8 – Indicates an admin operation performed in Azure Active Directory.
9 – Indicates OrgId logon events in Azure Active Directory. This record type is being deprecated.
10 – Indicates security cmdlet events that were performed by Microsoft personnel in the data center.
11 – Indicates Data loss protection (DLP) events in SharePoint.
12 – Indicates Sway events.
13 – Indicates DLP events in Exchange, when configured with a unified a DLP policy. DLP events based on Exchange mail flow rules (also known as transport rules) aren’t supported.
14 – Indicates sharing events in SharePoint.
15 – Indicates Secure Token Service (STS) logon events in Azure Active Directory.
18 – Indicates Security & Compliance Center events.
19 – Indicates aggregated Exchange mailbox operations for repetitive activity that occurs within a very short duration.
20 – Indicates Power BI events.
21- Indicates Dynamics 365 events.
22 – Indicates Yammer events.
23 – Indicates Skype for Business events.
24 – Indicates eDiscovery events. This record type indicates activities that were performed by running content searches and managing eDiscovery cases in the security and compliance center. For more information, see Search for eDiscovery activities in the Office 365 audit log.
25, 26, or 27 – Indicates Microsoft Teams events.
28 – Indicates phishing and malware events from Exchange Online Protection and Office 365 Advanced Threat Protection.
29 – Indicates submission events from Exchange Online Protection and Office 365 Advanced Threat Protection.
30 – Indicates Microsoft Power Automate (formerly called Microsoft Flow) events.
31 – Indicates Advanced eDiscovery events.
32 – Indicates Microsoft Stream events.
33 – Indicates events related to DLP classification in SharePoint.
35 – Indicates Microsoft Project events.
36 – Indicates SharePoint list events.
37 – Indicates events related to SharePoint comments.
38 – Indicates events related to retention policies and retention labels in the security and compliance center.
40 – Indicates events that results from security and compliance alert signals.
41 – Indicates safe links time-of-block and block override events in Office 365 Advanced Threat Protection.
42 – Indicates events related to insights and reports in the Office 365 security and compliance center.
44 – Indicates Workplace Analytics events.
45 – Indicates Power Apps events.
47 – Indicates phishing and malware events from Office 365 Advanced Threat Protection for files in SharePoint, OneDrive, and Microsoft Teams.
49 – Indicates Patients application events in Microsoft Teams for Healthcare.
50 – Indicates events related to the MailItemsAccessed mailbox audit action.
52 – Indicates events related to the Data Insights REST API.
53 – Indicates events related to the application of information barrier policies. For more information, see Define policies for information barriers.
54 – Indicates SharePoint list item events.
55 – Indicates SharePoint content type events.
56 – Indicates SharePoint list field events.
62 – Indicates events related to email attack campaigns. For more information, see Campaign Views in Office 365 ATP.
64 – Indicates automated investigation and response events. For information, see automated investigation and response (AIR) in Office 365
66 – Indicates Microsoft Forms events.
68 – Indicates Communication compliance events in Exchange. For more information, see Communication compliance in Microsoft 365.
69 – Indicates events related Customer Key Encryption. For more information, see Service encryption with Customer Key in Office 365.
