Secure Replication
September 2023
This Knowledge Base article provides an overview of the advanced security configurations Replicator supports. Security configurations are applied at multiple levels within Replicator, SharePoint and IIS. Replicator relies upon the security that is configured within your SharePoint farm first and foremost.
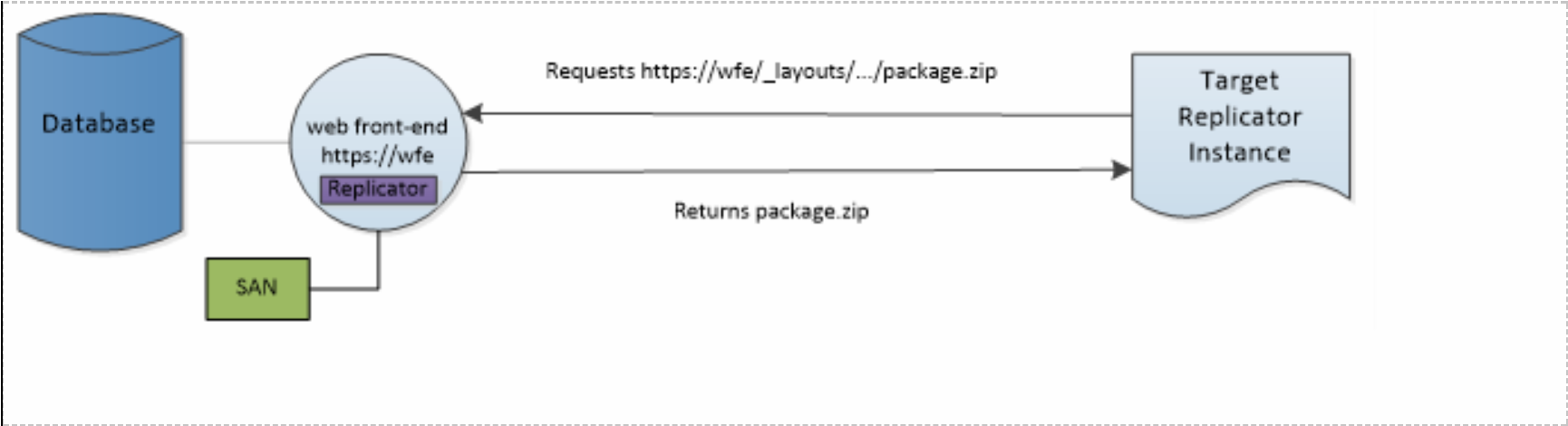
The following diagram demonstrates the various areas that can be secured when replicating packages between two web applications:
This document will reference the above diagram while providing an overview of Secure Replication.
Encrypting Transfers using HTTPS
Encrypting Transfers using Secure VPN
SharePoint
The first step to securing Replicator is to secure the SharePoint farm. The primary steps in securing a SharePoint farm are done through the configuration of secure connections and the use of least-privileged accounts.
Secure Connections
Secure connections can be configured for SharePoint by using the Hypertext Transfer Protocol Secure (HTTPS) option when creating or extending web applications. Another method to secure connections is to create a Virtual Private Network (VPN) connection between farms. These methods can be used separately or in tandem to enhance connection security.
Encrypting Transfers using HTTPS
The easiest method to secure SharePoint connections is through the use of the Hypertext Transfer Protocol Secure (HTTPS) which layers the HTTP protocol on top the Secure Socket Layer (SSL) and Transport Level Security (TLS) protocols. These protocols use system provided Windows functions to encrypts all inbound and outbound traffic for a web application at the Internet Information Services (IIS) level. Due to its unique design, Replicator leverages the security configuration of the underlying SharePoint platform. When the web application and its IIS web sites are configured to use HTTPS, all traffic to and from the web application is encrypted.
Replicator leverages this encryption through the use of the Binary Intelligent Transfer Service (BITS) as the transport layer between farms. After capturing an event on the source SharePoint farm, the content is packaged and then transferred using BITS. BITS transfers the package using the transfer protocol specified by IIS for the web application. When HTTPS is configured for the SharePoint web application this same level of encryption will be used by BITS to encrypt the transfer content.
This encryption and decryption of transfer content is handled entirely by IIS using the industry standards TLS and SSL. This provides administrators with a level of encryptions that is commonly understood with proven performance.